Listicle text included for screen readers:
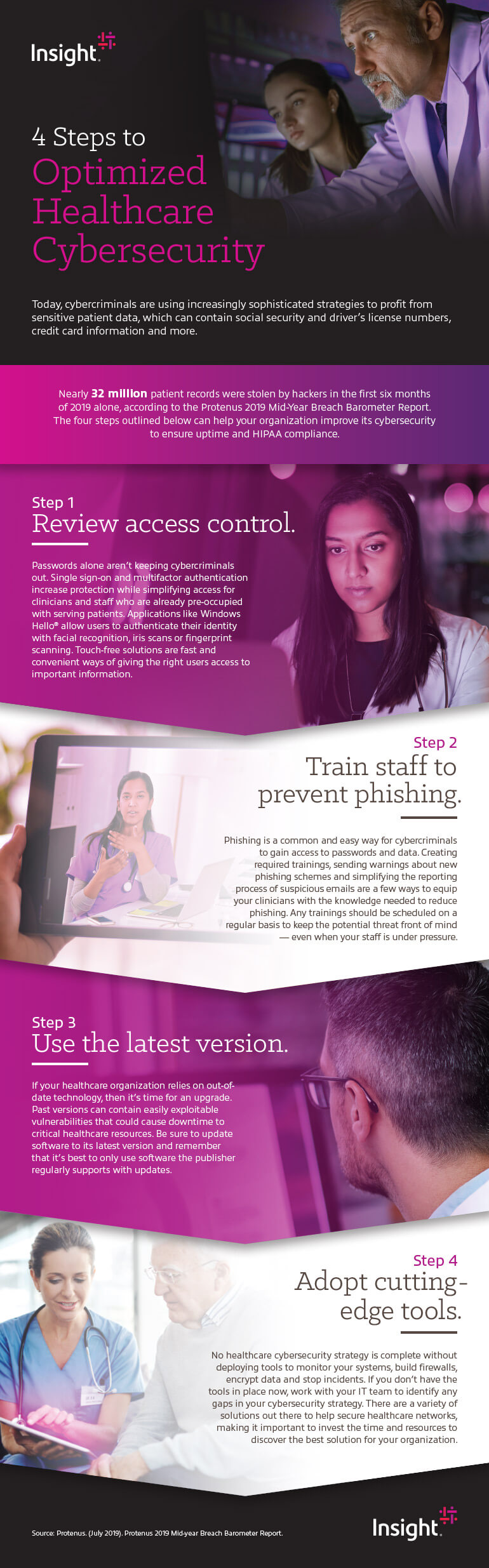
4 steps to optimized healthcare cybersecurity
Healthcare cybersecurity teams face many challenges from cybercriminals. They’re using increasingly sophisticated strategies to profit from sensitive patient data, which can contain social security and driver’s license numbers, credit card information and more.
Nearly 32 million patient records were stolen by hackers in the first six months of 2019 alone, according to the Protenus 2019 Mid-Year Breach Barometer Report. The four steps outlined below can help your organization improve its cybersecurity to ensure uptime and HIPAA compliance.
Step 1 — Review access control.
Passwords alone aren’t keeping cybercriminals out. Single sign-on and multifactor authentication increase protection while simplifying access for clinicians and staff who are already pre-occupied with serving patients. Applications like Windows Hello® allow users to authenticate their identity with facial recognition, iris scans or fingerprint scanning. Touch-free solutions are fast and convenient ways of giving the right users access to important information.
Step 2 — Train staff to prevent phishing.
Phishing is a common and easy way for cybercriminals to gain access to passwords and data. Creating required trainings, sending warnings about new phishing schemes and simplifying the reporting process of suspicious emails are a few ways to equip your clinicians with the knowledge needed to reduce phishing. Any trainings should be scheduled on a regular basis to keep the potential threat front of mind — even when your staff is under pressure.
Step 3 — Use the latest version.
If your healthcare organization relies on out-of-date technology, then it’s time for an upgrade. Past versions can contain easily exploitable vulnerabilities that could cause downtime to critical healthcare resources. Be sure to update software to its latest version and remember that it’s best to only use software the publisher regularly supports with updates.
Step 4 — Adopt cutting-edge tools.
No healthcare cybersecurity strategy is complete without deploying tools to monitor your systems, build firewalls, encrypt data and stop incidents. If you don’t have the tools in place now, work with your IT team to identify any gaps in your cybersecurity strategy. There are a variety of solutions out there to help secure healthcare networks, making it important to invest the time and resources to discover the best solution for your organization.
Protenus. (July 2019). Protenus 2019 Mid-year Breach Barometer Report.