Infographic 5 Steps to Better Data Security
Secure your most valuable information with these trusted solutions.
By Insight Editor / 16 Jul 2021 / Topics: Software
By Insight Editor / 16 Jul 2021 / Topics: Software
Data is the backbone of your modern business. It’s also one of the most vulnerable areas of your IT environment. Discover five crucial measures to ensure that your informational assets remain safe and secure.
Accessibility note: The infographic is transcribed below the graphic.
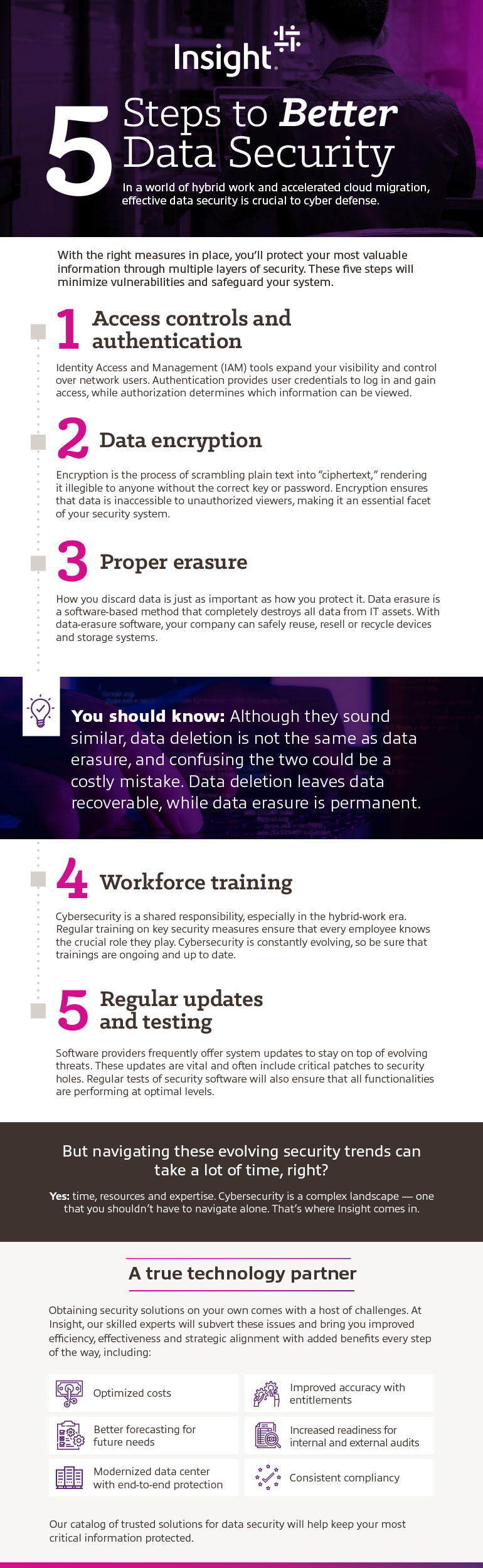
In a world of hybrid work and accelerated cloud migration, effective data security is crucial to cyber defense.
With the right measures in place, you’ll protect your most valuable information through multiple layers of security. These five steps will minimize vulnerabilities and safeguard your system.
1. Access controls and authentication
Identity Access and Management (IAM) tools expand your visibility and control over network users. Authentication provides user credentials to log in and gain access, while authorization determines which information can be viewed.
2. Data encryption
Encryption is the process of scrambling plain text into “ciphertext,” rendering it illegible to anyone without the correct key or password. Encryption ensures that data is inaccessible to unauthorized viewers — making it an essential facet of your security system.
3. Proper erasure
How you discard data is just as important as how you protect it. Data erasure is a software-based method that completely destroys all data from IT assets. With data-erasure software, your company can safely reuse, resell or recycle devices and storage systems.
You should know: Although they sound similar, data deletion is not the same as data erasure — and confusing the two could be a costly mistake. Data deletion leaves data recoverable, while data erasure is permanent.
4. Workforce training
Cybersecurity is a shared responsibility, especially in the hybrid-work era. Regular training on key security measures ensure that every employee knows the crucial role they play. Cybersecurity is constantly evolving, so be sure that trainings are ongoing and up to date.
5. Regular updates and testing
Software providers frequently offer system updates to stay on top of evolving threats. These updates are vital and often include critical patches to security holes. Regular tests of security software will also ensure that all functionalities are performing at optimal levels.
But navigating these evolving security trends can take a lot of time, right?
Yes: time, resources and expertise. Cybersecurity is a complex landscape — one that you shouldn’t have to navigate alone. That’s where Insight comes in.
A true technology partner:
Obtaining security solutions on your own comes with a host of challenges. At Insight, our skilled experts will subvert these issues and bring you improved efficiency, effectiveness and strategic alignment with added benefits every step of the way, including:
Our catalog of trusted solutions for data security will help keep your most critical information protected.

Discover reports, stories and industry trends to help you innovate for the future.