Listicle
Is Your Cloud Security Offering
These 3 Crucial Services?
By Insight Editor / 13 Dec 2022 / Topics: Cybersecurity
By Insight Editor / 13 Dec 2022 / Topics: Cybersecurity
Cyberattacks are on the rise. Learn how three key services offer ironclad protection against increasingly sophisticated attacks.
Accessibility note: The infographic is transcribed below the graphic.
Infographic text included for screen readers:
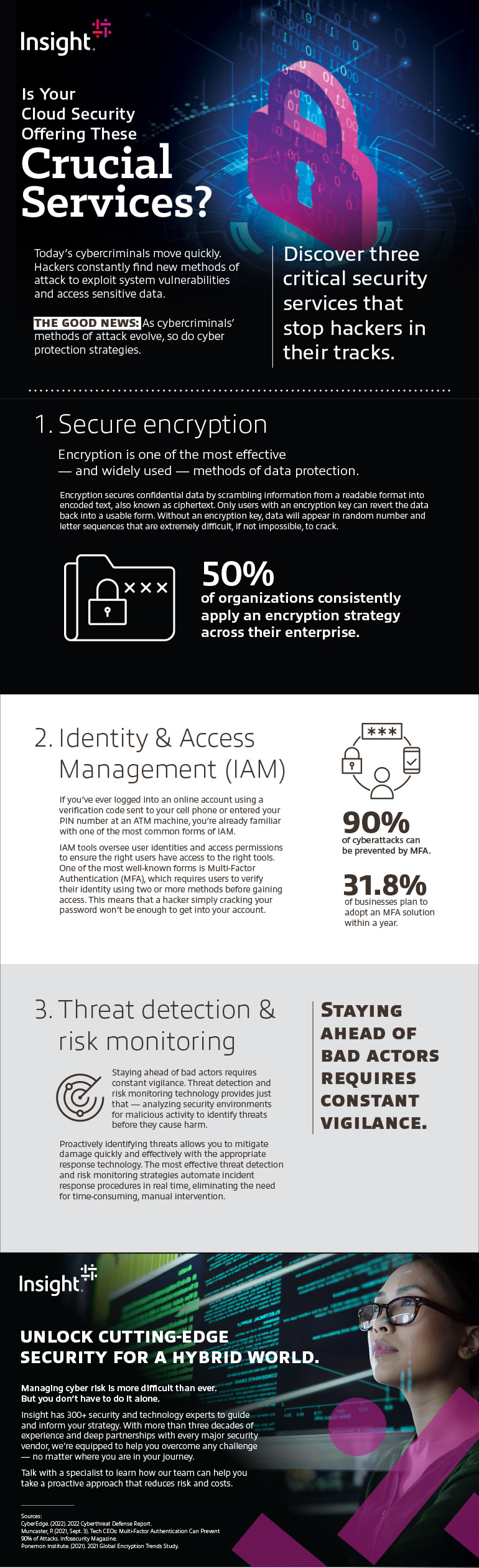
Today’s cybercriminals move quickly. Hackers constantly find new methods of attack to exploit system vulnerabilities and access sensitive data.
The good news: As cybercriminals’ methods of attack evolve, so do cyber protection strategies.
Discover three critical security services that stop hackers in their tracks.
Encryption is one of the most effective — and widely used — methods of data protection.
Encryption secures confidential data by scrambling information from a readable format into encoded text, also known as ciphertext. Only users with an encryption key can revert the data back into a usable form. Without an encryption key, data will appear in random number and letter sequences that are extremely difficult, if not impossible to crack.
50% of organizations consistently apply an encryption strategy across their enterprise.
If you’ve ever logged into an online account using a verification code sent to your cell phone or entered your PIN number at an ATM machine, you’re already familiar with one of the most common forms of IAM.
IAM tools oversee user identities and access permissions to ensure the right users have access to the right tools. One of the most well-known forms is Multi-Factor Authentication (MFA), which requires users to verify their identity using two or more methods before gaining access. This means that a hacker simply cracking your password won’t be enough to get into your account.
90% of cyberattacks can be prevented by MFA.
31.8% of businesses plan to adopt an MFA solution within a year.
Staying ahead of bad actors requires constant vigilance. Threat detection and risk monitoring technology provides just that — analyzing security environments for malicious activity to identify threats before they cause harm.
Proactively identifying threats allows you to mitigate damage quickly and effectively with the appropriate response technology. The most effective threat detection and risk monitoring strategies automate incident response procedures in real time, eliminating the need for time-consuming, manual intervention.
Unlock cutting-edge security for a hybrid world.
Managing cyber risk is more difficult than ever. But you don’t have to do it alone.
Insight has 300+ security and technology experts to guide and inform your strategy. With more than three decades of experience and deep partnerships with every major security vendor, we’re equipped to help you overcome any challenge — no matter where you are in your journey.
Talk with a specialist to learn how our team can help you take a proactive approach that reduces risk and costs.
Source:
CyberEdge. (2022). 2022 Cyberthreat Defense Report.
Muncaster, P. (2021, Sept. 3). Tech CEOs: Multi-Factor Authentication Can Prevent 90% of Attacks. Infosecurity Magazine.
Ponemon Institute. (2021). 2021 Global Encryption Trends Study.

Discover reports, stories and industry trends to help you innovate for the future.